What Is A Proxy Server? Deeply Detailed analysis
Introduce
In this digital age, safeguarding personal privacy and network security has become extremely important. Proxy servers, as a key player in the online world, have a significant role to play. Imagine it as an invisibility cloak that hides your real IP and keeps your online browsing more discreet. Moreover, it can speed up web page loading through caching, enhancing your internet experience. On the corporate side, proxy servers are also great for network management, content filtering, and security protection.
Whether you want to protect your online privacy or a business needs to control network access, proxy servers can provide solutions. Next, I'll take you through the basics of proxy servers, their main functions, applicable scenarios, advantages and disadvantages, and how to choose a suitable proxy server. This way, you'll have a clearer understanding of the value of this network tool and know how to utilize it better.
Basic Concepts of Proxy Servers
1. Definition of Proxy Server
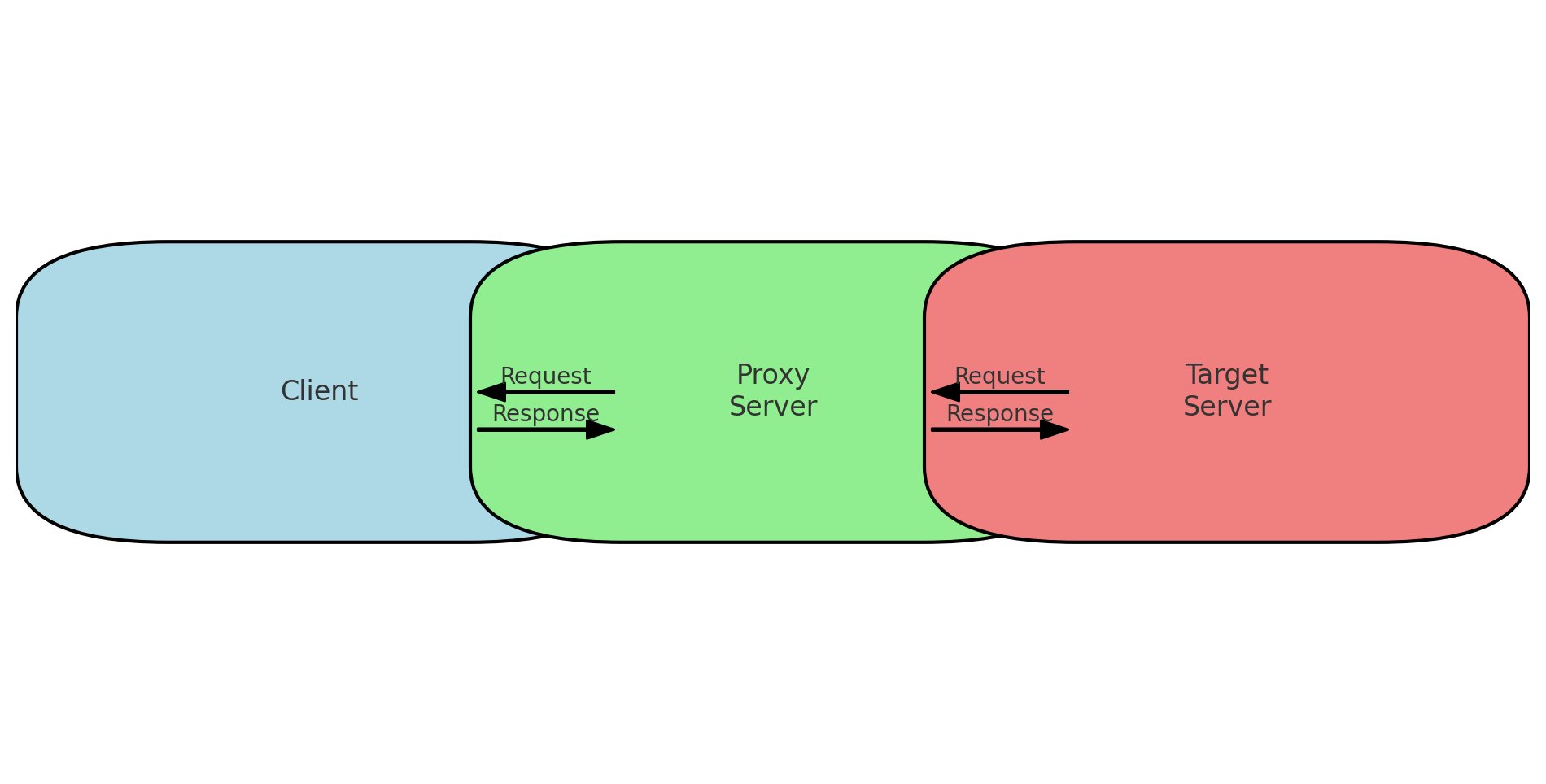
A Proxy Server is an intermediary server that sits between the client and the target server, assisting the client in sending requests and receiving responses. The client sends requests to the proxy server, which then forwards these requests to the target server on behalf of the client and returns the server's response back to the client. In this way, the proxy server conceals the client's real identity and can also process and manage the requests and responses.
2. Working Principle of Proxy Servers
The working principle of a proxy server is relatively straightforward: when a client, such as a browser, needs to access a website, it sends a request to the proxy server. After receiving the request, the proxy server makes the actual access request to the target server based on the content of the request. Once the target server processes the request, it sends the response back to the proxy server, which then relays the response to the client. Throughout this process, the target server only sees the IP address of the proxy server and not the real IP address of the client.
3. Basic Types of Proxy Servers
Forward Proxy A forward proxy is the most common type of proxy server, typically used to help clients access content that is blocked or restricted. The client explicitly specifies the use of a forward proxy to send requests, which then makes the request to the target server on behalf of the client. For example, a user who wishes to access a website that is blocked by their country or company can use a forward proxy to achieve this.
Reverse Proxy A reverse proxy is mainly used on the server side, positioned in front of multiple servers to receive requests from clients and then forward these requests to the internal servers for processing. Reverse proxy servers are commonly used for load balancing, caching content, and enhancing security. With a reverse proxy, a user's request can be distributed across different servers to alleviate the burden on a single server, improving the overall service's response time and reliability.
Proxy servers, through these basic concepts and types, provide flexible and effective solutions for different application scenarios, meeting users' various needs for privacy protection, access control, and performance optimization.
Main Functions of a Proxy Server
1. Providing Anonymity and Privacy Protection
A proxy server helps users maintain anonymity online by hiding their real IP addresses. This is particularly important for users who want to protect their personal privacy, especially when accessing sensitive websites or handling personal information. With a proxy server, users' online activities cannot be easily traced, thereby enhancing privacy protection.
2. Caching and Accelerating Network Requests
A proxy server can cache frequently accessed web content. When users request these contents again, the proxy server can provide responses directly from the cache without re-requesting from the target server. This caching mechanism not only reduces network bandwidth usage but also significantly speeds up access, improving the user browsing experience. For enterprises, the caching function of a proxy server can effectively reduce server load and increase network efficiency.
3. Controlling Network Access and Content Filtering
Network administrators can control and manage user access behaviors through a proxy server. For example, companies can use proxy servers to restrict employees from accessing unrelated or harmful websites, and schools can limit students' access to inappropriate content. Additionally, proxy servers can set different access permissions based on content type, user identity, or time periods, achieving more refined network management.
4. Enhancing Security
Proxy servers play a crucial role in enhancing network security. First, a proxy server can act as part of a firewall, filtering malicious traffic and blocking attacks. Second, proxy servers can protect transmitted data from eavesdropping and tampering through SSL/TLS encryption. Finally, some advanced proxy servers have the ability to defend against DDoS attacks by mitigating server load through traffic distribution and request validation, thus protecting network stability.
5. Load Balancing
In high-traffic environments, reverse proxy servers can distribute user requests to multiple servers for processing, thereby achieving load balancing. This method not only improves overall service availability and response speed but also enhances system fault tolerance and stability. Through load balancing, enterprises can utilize server resources more efficiently and provide better service quality.
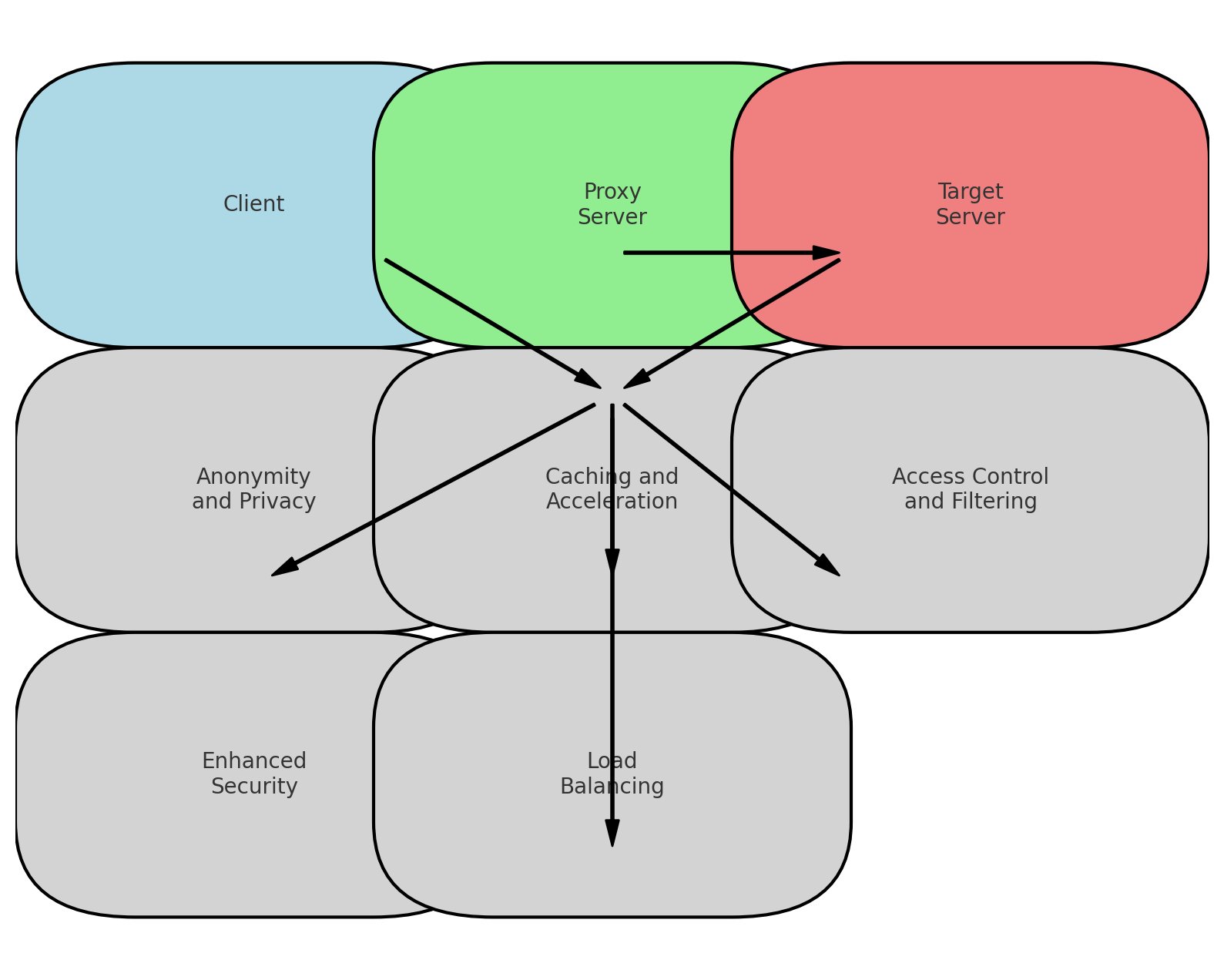
Proxy servers, through these various functions, provide powerful network access and management tools for both users and enterprises. In terms of privacy protection, network acceleration, access control, and security protection, proxy servers demonstrate irreplaceable value.
Application Scenarios
1. Enterprise Network Management
Access Control
Enterprises can use proxy servers to manage employees' network access permissions, preventing them from accessing non-work-related or potentially harmful websites. This not only helps improve work efficiency but also protects the enterprise network from potential threats.
Bandwidth Management
Through proxy servers, enterprises can optimize the use of network bandwidth. For instance, proxy servers can cache frequently used website content, reducing redundant network requests and saving bandwidth. Additionally, enterprises can set bandwidth limits via proxy servers to ensure that critical business applications receive sufficient network resources.
2. Personal Users
Anonymous Browsing
Personal users can hide their real IP addresses through proxy servers, protecting their privacy and preventing tracking. This is particularly useful when accessing sensitive information or protecting personal data on public networks.
Access Restricted Content
In some countries or regions, access to certain websites or content may be restricted. Personal users can bypass these restrictions using proxy servers, allowing them to access blocked websites or content. For example, users can access geo-restricted streaming services or social media platforms through proxy servers.
3. Data Collection and Web Scraping
Bypassing IP Blocks
Data collection and web scraping activities may encounter IP blocks from target servers when performing large-scale data retrieval. Using proxy servers can effectively circumvent this issue. By rotating different proxy IPs, data collection tools can continue to scrape data without being blocked by the target server.
Increasing Efficiency
Proxy servers can help distribute data collection requests, increasing overall efficiency. Multiple proxy servers working simultaneously can significantly speed up data retrieval, ensuring that data collection tasks are completed on time.
4. Network Security and Privacy Protection
Security Protection
Proxy servers can act as the first line of defense in network security, filtering malicious traffic and blocking unsafe requests from entering the internal network. Combined with firewalls and other security measures, proxy servers can significantly enhance network security.
Privacy Protection
By using proxy servers, users can hide their real IP addresses when accessing the internet, preventing personal information from being exposed. This is particularly important for users and businesses requiring high levels of privacy protection.
5. Educational Institutions
Content Filtering
Schools and educational institutions can use proxy servers to filter inappropriate content such as adult material or violent websites, ensuring that students learn and entertain themselves in a safe online environment.
Access Control
Through proxy servers, educational institutions can control students' internet usage time and access content, preventing students from visiting non-educational websites during class time and improving classroom efficiency.
Proxy servers play an important role in these various application scenarios, not only enhancing network efficiency and security but also providing users with flexible network access solutions. Whether for enterprises, personal users, or educational institutions, proxy servers can meet their specific network management and usage needs.
Advantages and Disadvantages of Proxy Servers
Advantages
1. Enhanced Security
Proxy servers can serve as an additional layer of security by filtering harmful traffic, blocking malware, and protecting against cyber threats such as Distributed Denial of Service (DDoS) attacks. They act as a barrier between the internal network and external threats, ensuring a safer online environment.
2. Improved Browsing Speed
By caching frequently accessed web content, proxy servers can significantly speed up browsing. When users request cached content, the proxy server can deliver it quickly without having to re-fetch it from the original server. This not only enhances user experience but also reduces load times.
3. Privacy Protection
Proxy servers help protect user privacy by masking the user’s IP address. This makes it difficult for websites and third parties to track users’ online activities. Anonymity is particularly beneficial for users who are concerned about privacy and data security.
4. Access to Restricted Content
Users can use proxy servers to bypass geographical restrictions and censorship, allowing them to access websites and services that may be blocked in their region. This is particularly useful for accessing streaming services, social media, and other region-locked content.
5. Load Balancing
In high-traffic environments, proxy servers can distribute incoming traffic across multiple servers to balance the load. This ensures that no single server is overwhelmed, improving the overall performance and reliability of the network.
Disadvantages
1. Potential Performance Bottlenecks
If a proxy server is not properly managed or lacks sufficient resources, it can become a performance bottleneck. This can lead to slower browsing speeds and increased latency, negatively affecting the user experience.
2. Added Complexity
Implementing and managing proxy servers adds an extra layer of complexity to network infrastructure. Proper configuration and maintenance are required to ensure they function correctly and do not introduce vulnerabilities or inefficiencies.
3. Possible Reliability Issues
Not all proxy servers are equally reliable. Some free or poorly maintained proxy servers may be unstable, leading to frequent downtimes or connection issues. This can disrupt network access and reduce overall reliability.
4. Security Risks from Untrusted Proxies
Using untrusted or unknown proxy servers can pose significant security risks. These proxies might log user activities, inject malicious code, or expose users to phishing attacks. It is crucial to choose reputable and secure proxy providers to mitigate these risks.
5. Limited Features in Basic Proxies
Basic proxy servers might offer limited features compared to more advanced solutions. For instance, they may lack sophisticated caching mechanisms, advanced security features, or comprehensive access control options, making them less effective in certain scenarios.
Proxy servers offer numerous benefits, including enhanced security, improved browsing speed, privacy protection, access to restricted content, and load balancing. However, they also come with potential drawbacks such as performance bottlenecks, added complexity, reliability issues, security risks from untrusted proxies, and limited features in basic proxies. Weighing these pros and cons is essential when deciding whether to implement a proxy server and which type to choose based on specific needs.
How to Choose the Right Proxy Server
Selecting the right proxy server depends on several factors, including the specific needs of the user, performance requirements, security considerations, and cost. Here are some key points to consider when choosing a proxy server, with a recommendation for LightNode VPS services.
1. Determine the Purpose
Understanding the primary use case for the proxy server is crucial. Whether it’s for personal privacy, enterprise security, data collection, or accessing restricted content, different purposes may require different types of proxy servers (e.g., residential proxies, data center proxies, or reverse proxies).
2. Evaluate Performance
Performance is a critical factor. Look for proxy servers that offer high-speed connections, low latency, and high uptime. Performance can significantly impact user experience and the effectiveness of the proxy server in tasks such as web scraping or streaming content.
3. Assess Security Features
Security is paramount, especially for enterprise use. Ensure the proxy server offers robust security features such as SSL/TLS encryption, IP whitelisting, and traffic filtering. For sensitive applications, consider proxies that provide advanced security measures to protect against cyber threats.
4. Consider Global Coverage
For users who need to access content from different regions or distribute network load globally, it’s essential to choose a proxy server with a broad geographical presence. This ensures optimal performance and access to geo-restricted content.
5. Pricing and Cost Efficiency
Cost is always a consideration. Look for proxy services that offer transparent pricing and good value for money. Hourly billing can be advantageous for users who need flexible and scalable solutions without long-term commitments.
6. Customer Support and Reliability
Reliable customer support can be a lifesaver when issues arise. Choose proxy services with a reputation for excellent customer service and support. Reliability in terms of server uptime and consistent performance is also critical.
Recommendation: LightNode VPS
If you're looking for a reliable and efficient proxy server solution, LightNode VPS is an excellent choice. Here’s why:
Key Features of LightNode VPS:
- Global Coverage: LightNode VPS servers are available in 42 locations worldwide, ensuring excellent coverage and access to geo-restricted content from virtually anywhere.
- Hourly Billing: LightNode offers flexible hourly billing, allowing you to pay only for the resources you use. This is ideal for users who need scalable solutions without committing to long-term contracts.
- High Performance: LightNode VPS provides high-speed connections and low latency, making it suitable for tasks that require quick and reliable network access.
- Excellent Customer Support: With a strong reputation for reliable customer service, LightNode ensures that any issues you encounter are quickly and efficiently resolved.
Steps to Choose LightNode VPS:
- Identify Your Needs: Determine whether you need the VPS for personal use, enterprise security, data collection, or accessing restricted content.
- Choose a Location: Select from LightNode’s 42 global locations to optimize performance and access the necessary regions.
- Select a Plan: Based on your usage requirements, choose a plan that fits your needs. LightNode’s hourly billing ensures flexibility and cost-efficiency.
- Monitor Performance: Regularly monitor the performance of your VPS to ensure it meets your expectations and adjust your plan as needed.
Future Trends of Proxy Servers
The landscape of proxy servers is continually evolving, driven by advancements in technology, increasing demands for privacy and security, and the need for improved network performance. Here are some key trends shaping the future of proxy servers:
1. Enhanced Security Measures
As cyber threats become more sophisticated, proxy servers will integrate advanced security features to provide robust protection. Future proxy servers are likely to include enhanced encryption methods, AI-driven threat detection, and real-time monitoring to prevent data breaches and cyberattacks.
2. Greater Emphasis on Privacy
With growing concerns over data privacy, future proxy servers will focus more on user anonymity and data protection. Innovations may include decentralized proxy networks that minimize the risk of data interception and ensure that users' activities remain private.
3. Increased Use of AI and Machine Learning
Artificial intelligence (AI) and machine learning will play a significant role in the development of proxy servers. These technologies can optimize traffic routing, predict and mitigate potential threats, and manage large-scale proxy networks more efficiently. AI-driven proxies can also learn user behavior patterns to provide more personalized and effective services.
4. Expansion of Cloud-Based Proxies
The shift towards cloud computing will continue to influence the proxy server market. Cloud-based proxy solutions offer scalability, flexibility, and ease of management, making them an attractive option for businesses of all sizes. This trend will likely lead to the development of more sophisticated cloud proxy services with enhanced capabilities.
5. Rise of Zero Trust Network Architecture
Zero Trust Network Architecture (ZTNA) is an emerging security model that assumes no network, whether internal or external, is trustworthy. Future proxy servers will align with ZTNA principles, ensuring that every request is authenticated and authorized, thereby enhancing security and reducing the risk of unauthorized access.
6. Growth of Edge Computing
Edge computing involves processing data closer to the data source rather than relying solely on centralized data centers. Proxy servers will increasingly be integrated into edge computing infrastructures to reduce latency, improve performance, and provide real-time data processing capabilities, especially for IoT devices and applications requiring immediate responses.
7. Improved Performance and Speed
As internet speeds continue to increase and more data is transmitted online, proxy servers will need to keep pace. Future proxies will leverage faster hardware, more efficient caching algorithms, and better load balancing techniques to handle increased traffic and provide faster, more reliable connections.
8. Integration with Other Technologies
Proxy servers will increasingly be integrated with other technologies, such as VPNs, firewalls, and content delivery networks (CDNs), to provide comprehensive solutions for security, privacy, and performance. This integration will offer users seamless and multi-layered protection against various online threats.
Conclusion
The future of proxy servers is bright, with numerous advancements on the horizon aimed at enhancing security, privacy, performance, and integration. As technologies such as AI, edge computing, and cloud services evolve, proxy servers will become even more vital in providing secure, efficient, and reliable network solutions for both individuals and businesses. Staying abreast of these trends will ensure that users can leverage the latest developments to meet their evolving needs and challenges in the digital age.
